Maybe the TJ MAXX breach didn’t scare you because you don’t shop there.
Maybe the Target breach didn’t scare you because you don’t shop there.
Maybe the Yahoo breach didn’t scare you because you never opened an account.
The RNC data breach probably didn’t scare you, even though Time and other outlets report the information contained date of birth along with your address and an RNC ID, simply because you never heard of it, but, 198 million of you should have been damned scared.
The Equifax breach should have scared to the point pee is running down your leg. Just because you weren’t contacted by Equifax to let you know doesn’t mean your data wasn’t taken. Click that link and read the story in “USA Today.” That 143 million number you see bantied about, it’s just a starting point and Congress knows it.
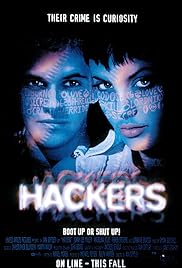
Here’s the dirty little secret with data breaches. You never really know how much was taken. Log files don’t exist forever, only a certain number of months, up to a few years. Just because you found one source of a breach, doesn’t mean you found every source of stupidity and greed at your company. Rent the movie “Hackers.” There is a great scene in there where one character rants about the “most commonly used passwords.”
Why do I want you to rent that movie and pay attention to that scene? So you will think about how such a list comes to be. Seriously, think about it. Some, possibly random, group of system managers pulls and decrypts all of the passwords on their system, puts them into a file and sends them to some supposedly honorable and secure “security research” facility in what is reported to be an anonymous fashion.
Why am I speaking so vaguely? Well, because any “security research” firm reputable enough to trust with that level of information is probably working for/with the NSA. Oh, you probably didn’t pay attention to the NSA breach/hack.
Think about how the tiniest slip, such as identifying information as to which company a password file came from, now gives a crime organization with a bot-net two thirds of what they need. They just have to guess the account names and some of them will be standard.
I understand, the intent of generating the most common passwords list is so system managers can ban the use of said passwords, theoretically making systems more secure, but, what is needed to create said list is the IT equivalent of nuclear weapons.
Don’t expect Facebook, Google or insert-Internet-company-name-here to keep your data safe. It ain’t going to happen. Most likely there is already a parasite inside their systems nibbling away at data, just a couple of records at a time, slowly fed to a very patient collector.
While I have worked in IT for over 30 years, I have only dabbled in the system security side of life. What I do know is that data from the really big breaches by the Uber nasty groups does not get offered for sale until _after_ all access is lost. These players are in it for the long haul. When the first batch of records get sold all kind of identity theft and security monitoring groups start trying to triangulate where the data could have come from. Selling the data shortens your access, hence, the smart ones hoard the data until they get found out.
Keep in mind, some of these groups steal it for themselves. It won’t be for sale on the Dark Web.
The NSA breach is disturbing because tools and techniques were taken. This means even the stupid hackers can suddenly be smart, for a price.