Today even people who know nothing about computers have heard of hackers, ransomeware, and spyware. There was even a very funny Dick Tracy comic strip in the 1970s where this scruffy old guy visits a doctor’s office complaining of his systems and in the last frame says
Give it to me straight doc! Have I got one of them Computer Viruses?
scruffy old guy
Hollywood created the greatest computer hacking movie of all time in 1995 with Hackers.
It wasn’t just the actors or the special effects. The script didn’t reach too far. This was the era of dial-up access and users with stupid passwords like “God” and “Password_1234.” This movie is so good it has now become part of the problem. Everybody has that quaint “kids just having fun” notion of hackers in their mind.
Security Has Been a Problem Since Computers Connected
We used to lock computers inside a data center in corporate headquarters. Data came in via keypuch operators, paper cards, or 2400 foot magnetic tapes. Access to the actual room was controlled by all manner of keypad/button locks on doors.
This security was above and beyond the facilities “general security” of guards, ids, etc. Most data centers tended to have multiple computer operators at night and a large staff during the day. Going unnoticed was difficult and you had to carry around those 2400 foot tapes or an expensive drive pack. Then companies started hooking up modems.
I talk a lot about this history in my Agile book. I’ve even blogged about Security Via Obsolescence.
Today’s Massive Breaches Started With Agile
You’ve all got your favorite breach. Maybe the recent Ascension breach shut down your surgery/doctor visit? Maybe, like me, you think it is hilarious that in 2013 Google was outraged by NSA hacking of it? In 2017 I wrote about of some of the bigger more famous ones like Target, TJ MAXX, Equifax.
This isn’t “Just a way of life,” this is bad management.
Agile is embraced by Corporate America to commit accounting fraud. (I also cover this topic in my Agile book.) It’s a series of meaningless rituals to justify hacking on the fly and to end-run Sarbanes-Oxley accounting regulations. You need to watch Enron: The Smartest Guys in the Room.
During the days of Enron companies paid to get sky-high evaluations of non-functional custom software to “cook the books.” During the days of Agile companies use high internal chargebacks with “automated testing” to end-run SOX. This cooks the books generating sky-high values for non-functioning software. It’s one of the reasons a Sprint is only two weeks. Every two weeks you have a big jump in “book value.”
Cooking the Books Requires Relentless Bottom Line Focus
To do this effectively management needed low wage workers and a way to cover up complete failure. Agile allows both. Without any written definition of what the final product really is supposed to do nobody can say it failed. It “just has bugs.” With actual Software Engineering you have a detailed specification in the SDLC. It’s quite obvious when you leave a steaming pile on the new carpet.
Management’s obsession with paying low wages has created countless security breaches and financial loses. The off-shoring of IT jobs to people whose only qualification was being “priced right” lead to an epidemic of Grade 8 Bolt Syndrome which was required to justify it.
The Most Expensive Thing You Can Have is Cheap Labor
Read that heading again. Burn it into your mind. MBAs, especially those from shit schools like Keller, naturally have a focus on cheap labor to “cut costs.” Growing the business to improve the bottom line would require actual management. We can’t have that now!
It’s not just MBAs that are stupid in this regard. I’ve seen farmers be just as dumb.

Out on my 4-mile walk back in 2022 I came across this scene of where hired help drove a planter out of a field across the road ditch. Doesn’t look too bad from that angle with me standing down in the ditch does it?

How about from this angle? I need to point out they had something like a 48 or 60-row planter.

That picture really doesn’t convey the width of the thing. Those bars running back at an angle are where it folds forward for transport. You don’t have to be a physical engineer to realize that is a really long steel beam running from the hitch of the tractor back to the center beam running across all rows.

How about after the ditch is mowed? Adding insult to injury that spot between the telephone poles that looks un-mowed is the field entry. There is a culvert where it is level-ish to go in and out of the field. It wasn’t 60 feet from where this happened.
Why This Story?
I’m giving all of you non-farmers these details because less than two miles down the road, while moving at transport speed the planter disconnected from the tractor. It bent at least half a dozen or more row units, long shafts and most likely tweaked the frame/center beam. Planters like these cost way north of $100K. Planters, like cars, once the frame is bent, are never quite right again. That is the one part you really can’t replace.
It just broke going down the road.
Story that got put out
No, it broke when your $8/hr labor drove it through that ditch. It just took a few miles to actually come apart.
Focus on Cheap Labor is Deadly
Cheap labor is how you get stories like this one with dead bodies. The planter story could have been a lot worse if it came apart in the middle of an intersection with traffic.
Cheap labor, especially off-shore/visa-worker labor whose only real qualification is being “priced right” cause data breaches. In an effort to artificially inflate the bottom line both management and unqualified developers refuse to admit most systems are too big to Agile. Not “some,” most.
Agile’s complete banishment of actual Software Engineering along with System and Application Architects leads to consumers being spied on in their own homes via big-name products. MBAs believing they can “cut costs” by moving to “the cloud” concentrate a trove of your identity, financial, and medical information in a central place. They’ve been spewing this tale that “the cloud” is secure.
Just who do you think staffs the data centers where “the cloud” is hosted? The cheapest labor they can find.
Just remember, SolarWinds is the company producing the VPN/security software used by the government for very sensitive database access in agencies like the FBI, NSA, etc. Obviously their data center is also staffed by cheap labor that didn’t bother to secure the automatic update server.
Hackers Won’t Have to Break In Anymore
What caused this lengthy post to jump from my mind was a job post that came to my attention. I do C++ Embedded Linux with Yocto work so things like this find their way to me. The general description didn’t look too bad.
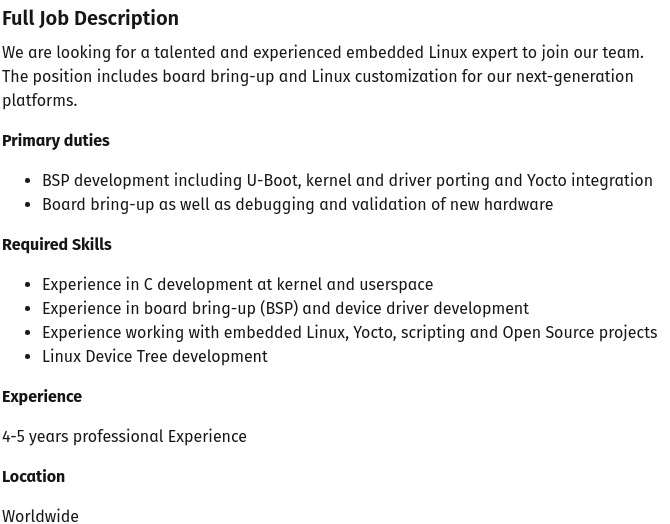
Then I looked at the pay.

Yocto people working with C/C++ on embedded Linux are scarce. Every medical device, IoT, automotive, agricultural, and even appliance manufacturer is looking for them. Even taking into account the 100% remote aspect of this, the “cheap” rate is $80/hr on 1099. Most are over $100/hr because they are just swamped with work.
What Do You Get With This Rate?
Most of you will say someone that is not qualified. Most of you will be wrong. They will get someone highly qualified from Fancy Bear, Cozy Bear, Lazarus Group, or some other hacker group on this list. I’m not going to name the company, but they make stuff that gets used in both medical device and military systems. They should know better! Seeing this really pissed me off.
Agile ensures the work of these individuals will go un-noticed. Those “team code reviews” are nothing more than a quick scan to see you followed formatting and naming conventions. Management is constantly pushing for developers to complete more User Stories and since you don’t have a System Architect running rough-shod over developers, there is nothing to stop malicious code.
All code has to do to make it into production under Agile is pass the automated tests.
The hackers are taking advantage of price-focused incompetent management. They fund these people via ill-gotten gains from identity theft, ransomeware, etc. The new breaches will be baked into the products from the factory.
I’m not some conspiracy theory nutter. The NSA has already found this in routers.
Summary
Hackers get in due to management’s maniacal focus on finding “priced right” labor not caring who gets hurt as long as this quarter’s numbers look good.
For the non-technical people, this is what the use of Agile and maniacal pursuit of the bottom line cause.

